Blue Team Labs Online - Cov

Analysts reported that red teamers bypassed the AV’s using AMSI techniques, added exclusions to AV and maintained a foothold.
Reverse Engineering
Tags: dnSpy CyberChef OSINT T1219 T1562
Scenario The Security Operations team was working on the data generated from a recent Red Teaming Engagement. Analysts reported that red teamers bypassed the AV’s using AMSI techniques, added exclusions to AV and maintained a foothold. Log Analysis was carried by analysts. Forensics team sent 3 samples to the RE team to identify any key characteristics and deduce IoC’s.
Note: In questions, S1 means Sample1, S2 means Sample2, S3 means Sample3.
Environment Awareness
Evidence & Tool Discovery
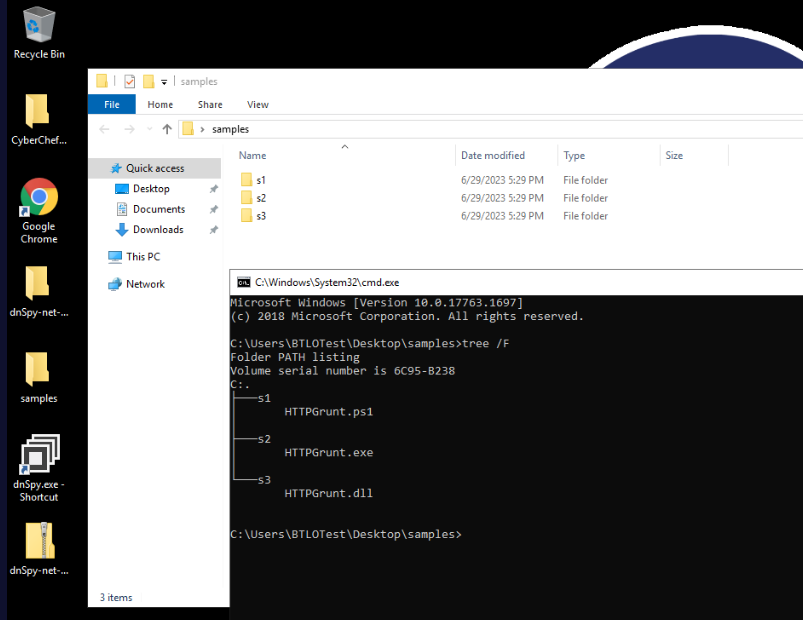
We were provided with 3 samples of this malware with different type of files from PowerShell script (ps1), PE32 executable (exe) and dynamic link library (dll) which only dnSpy and CyberChef available which indicates that we are working with .NET compiled binary.
Investigation
Q1) S1: What is the C2 IP address and port? (Format: x.x.x.x:port)
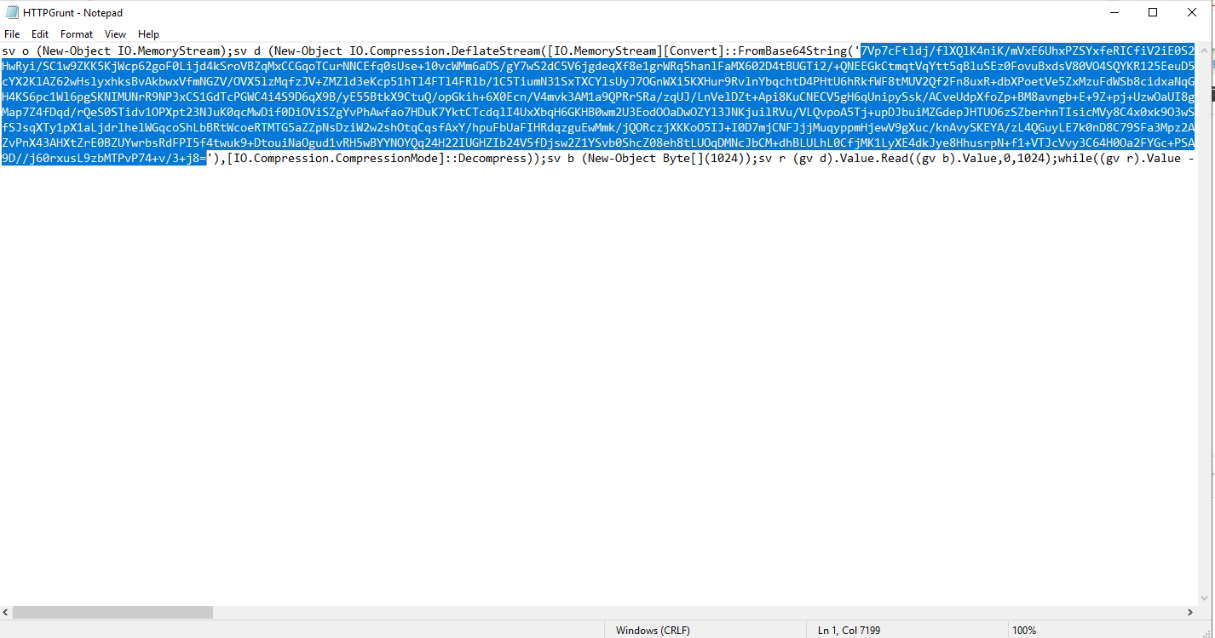
Lets start with sample 1 (ps1) then we could see that its a script that will create and execute stage 2 payload from this base64 string so lets decode it with base64 and extract it from zlib compression.
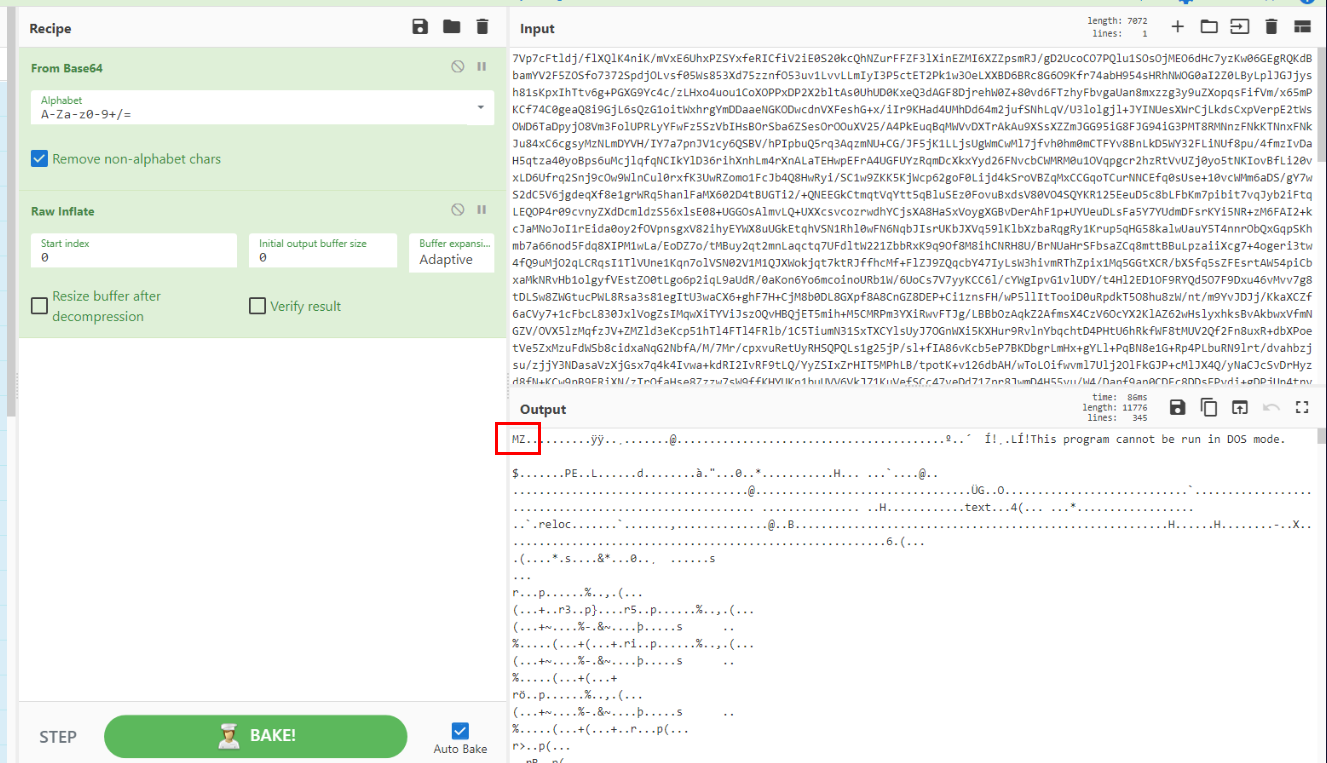
Then we will have stage 2 payload right here.
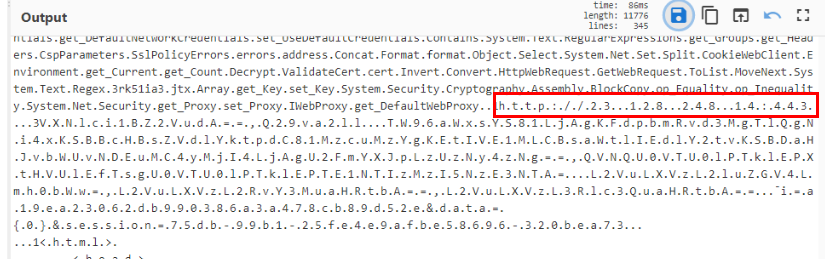
Scrolling for a bit then you will see C2 url that will be contacted by this payload.
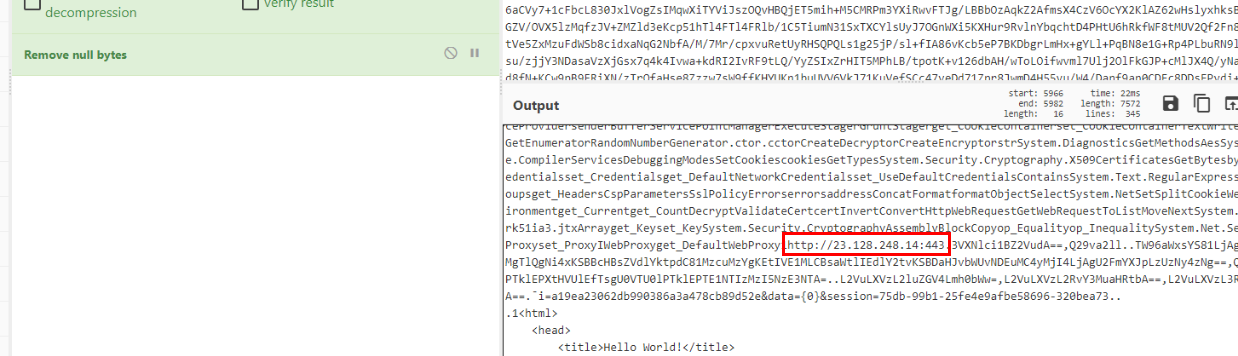
Add remove null bytes so we can directly copy CyberChef output.
Answer
23.128.248.14:443Q2) S2: What is the compiled date of the executable? (Format: DD/MM/YYYY)
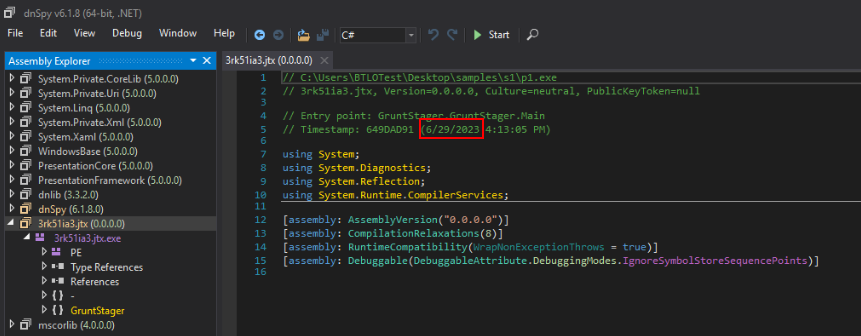
Open dnSpy and let it decompile sample 2 (I was mistaken since I thought it asked for S1 but all good since all of these payload generated by the same C2 on the same date)
Answer
29/06/2023Q3) S2: What is the C2 IP address and port? (Format: x.x.x.x:port)
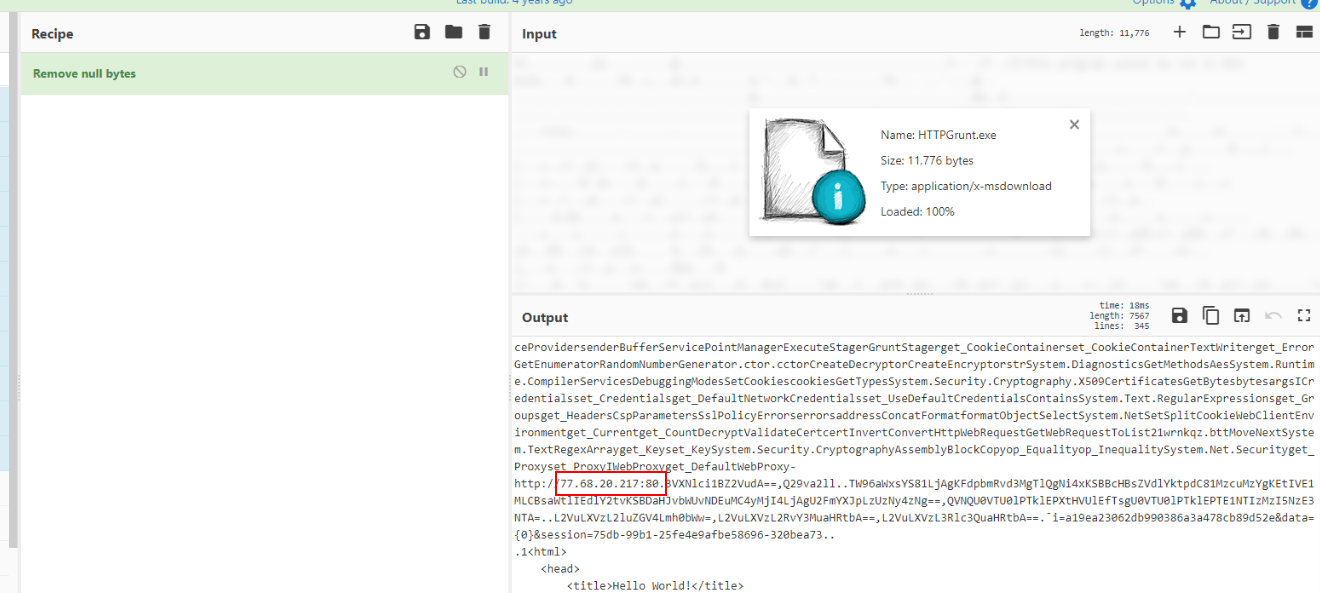 You can find it on dnSpy but I wanted to try if CyberChef still works, and sure enough it is!
You can find it on dnSpy but I wanted to try if CyberChef still works, and sure enough it is!
Answer
77.68.20.217:80Q4) S3: What is the C2 IP address and port? (Format: x.x.x.x:port)
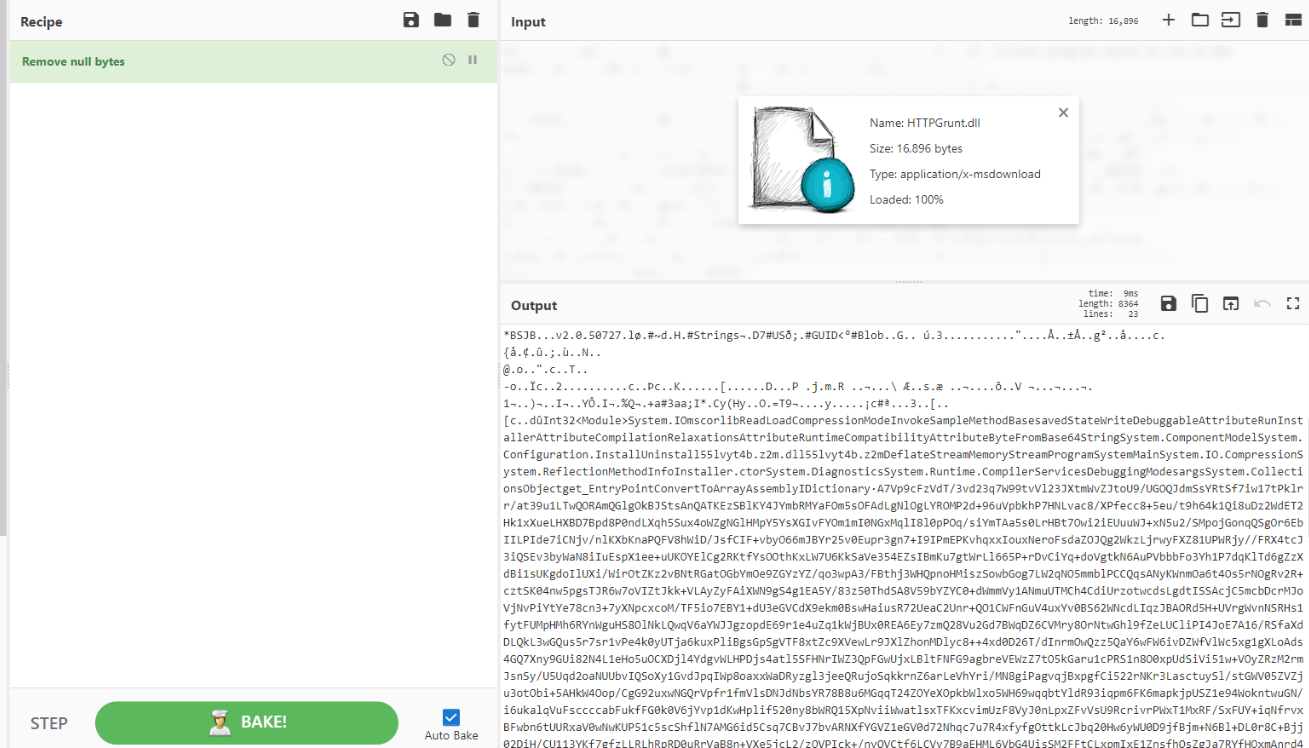
I tried to get anything useful with CyberChef but then look like we need to get this base64 string from dnSpy and decode it.
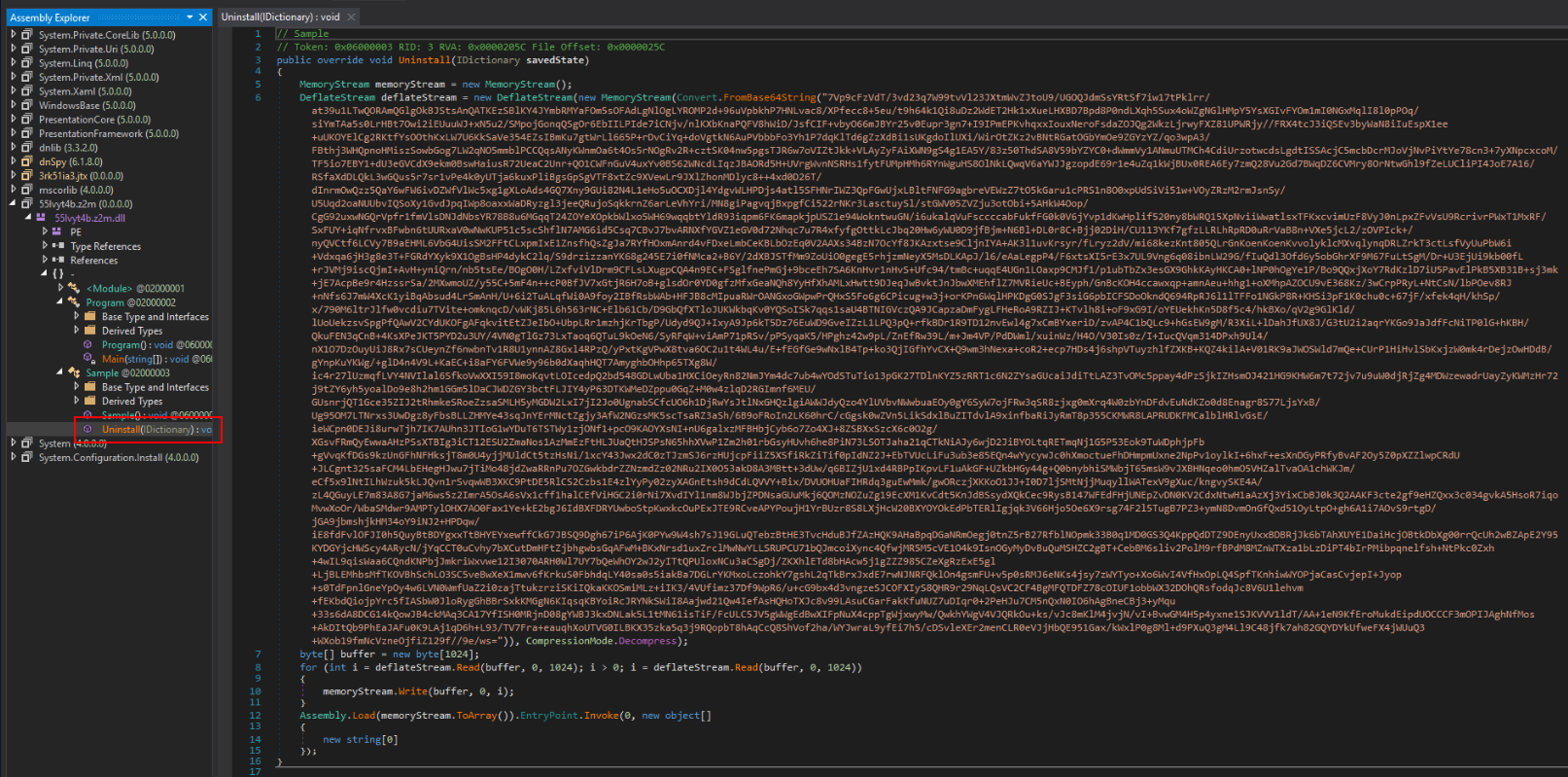
This base64 string reside in Uninstall function and we could use the same recipe as we did to S1 to extract second payload which contains C2 address and port.
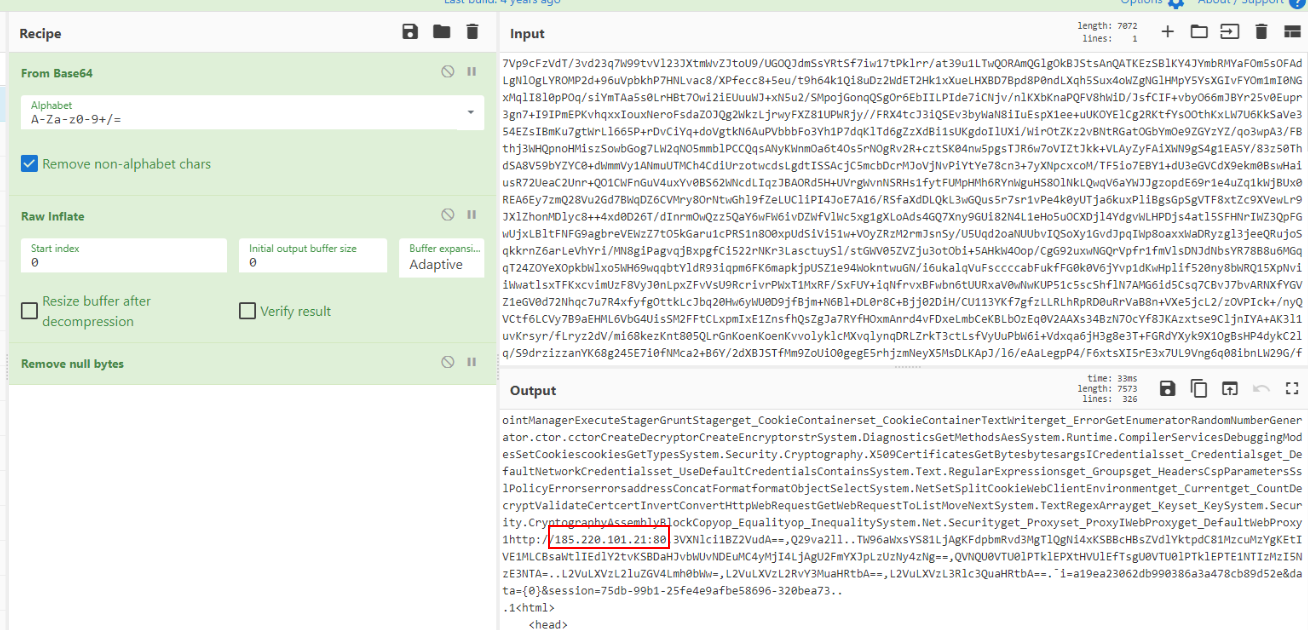
There it is!
Answer
185.220.101.21:80Q5) What is the C2 framework behind the generation of these samples? (Hint: Source Code) (Format: Framework Name)
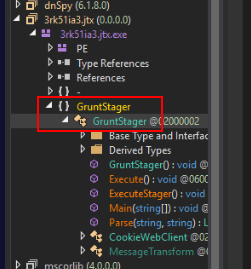
After taking a look at decompiled binary, we can see that its Grunt HTTP Stager
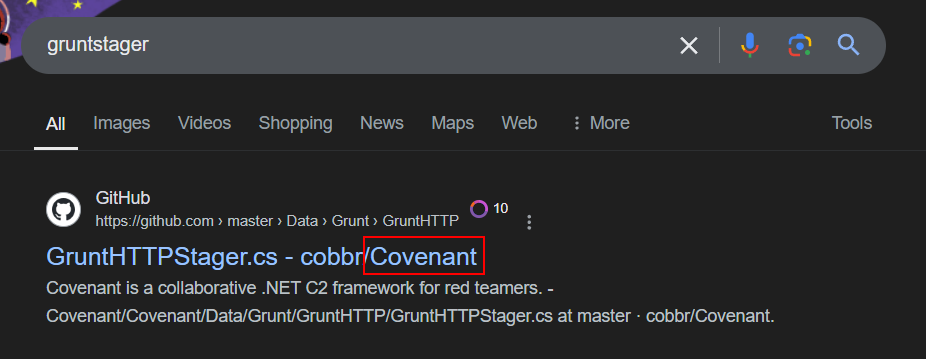
Which is a stager created by Covenant C2 framework.
Answer
Covenant https://blueteamlabs.online/achievement/share/52929/146
https://blueteamlabs.online/achievement/share/52929/146